News & Articles

Is Your Firewall Ready for NIS2?
1. Why the spotlight is suddenly on your firewall The EU’s NIS2 Directive (Directive (EU) 2022/2555) came into force in...
Pablosec Becomes an Official Arctic Wolf® Partner—Bringing World‑Class Security Operations to Your Doorstep
Today we’re thrilled to announce that Pablosec has joined the Arctic Wolf® Partner Program, expanding our ability to help...

The End of the SSL VPN Era: FortiOS 7.6.3 Marks a Turning Point
Fortinet has officially ended support for SSL VPN tunnel mode in FortiOS 7.6.3, signaling a significant shift in remote access...

Pablosec Solutions Joins Guaranteed Irish: Building a Sustainable Future Together
We are excited to share that Pablosec Solutions has officially joined Guaranteed Irish, a prestigious organization that...

A New Chapter: Joining Cyber Tech Accord to Advance Cybersecurity and Innovation
I'm thrilled to announce that I have joined CyberTechAccord.org—a dynamic community of professionals dedicated to advancing...
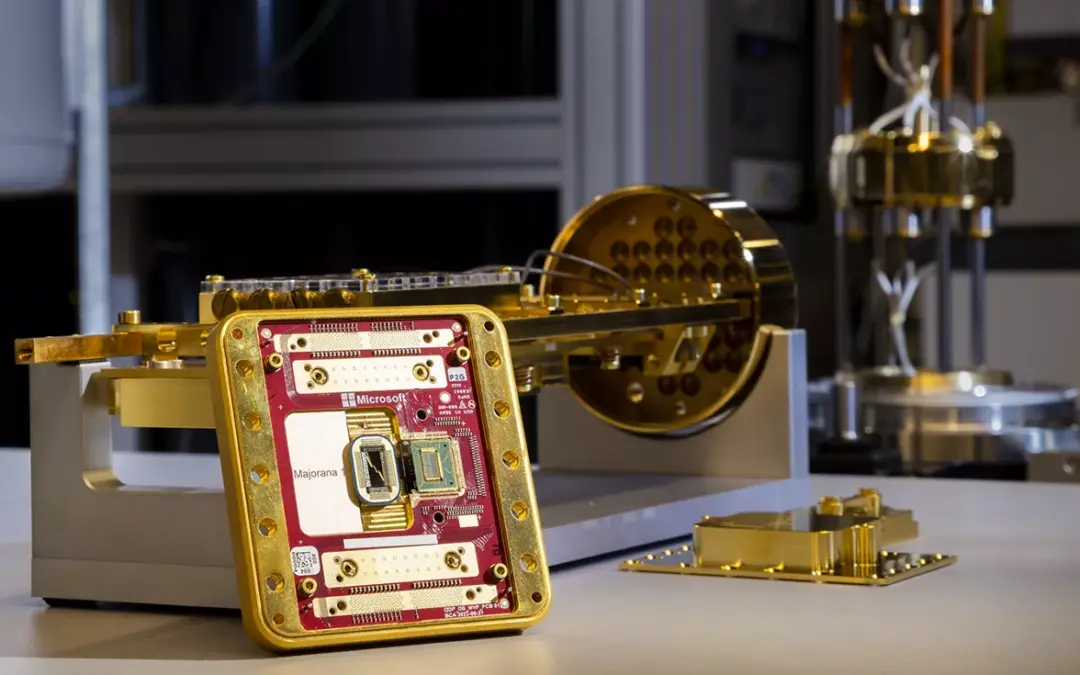
Securing Tomorrow’s Data Today: Why IPsec Needs Post-Quantum Cryptography
In the rapidly shifting world of cybersecurity, staying one step ahead of emerging threats is an ongoing challenge. Ransomware,...

Upgrade Your Network Security with the FortiGate G-Series NGFW
Is your network still protected by a legacy firewall? If so, it might be time to consider an upgrade. Many of the legacy...

Pablosec Joins South Dublin Chamber to Strengthen Local Business Collaboration
We are pleased to announce that Pablosec has joined the South Dublin Chamber, an organization dedicated to supporting the growth...

Are Your Employees Using DeepSeek Right Now? 🚨
Are Your Employees Using DeepSeek Right Now? 🚨 DeepSeek, a Chinese AI application, stores user data on servers in China, raising...
Fortinet Extends SSL VPN Removal to Most Desktop Models in FortiOS 7.6.1
Fortinet has announced that SSL VPN functionality will be removed from a wide range of desktop and rugged FortiGate and...
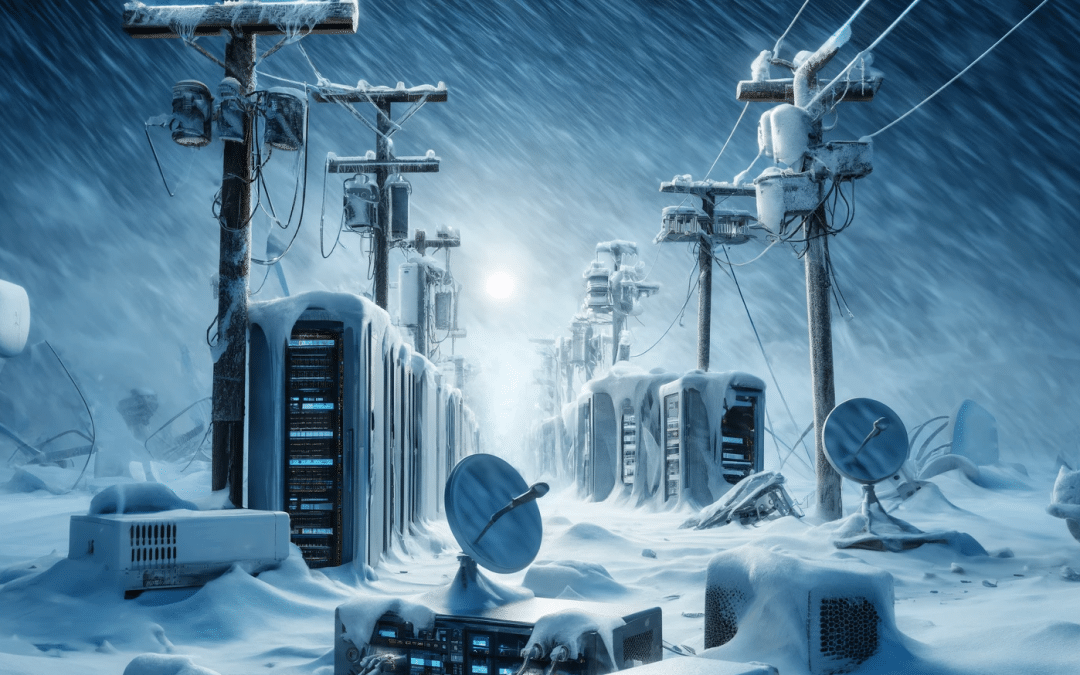
Ensuring Business Continuity During Extreme Weather with SD-WAN Solutions
Ensuring Business Continuity During Extreme Weather with SD-WAN Solutions This weekend, an intense snowstorm has been sweeping...

Detecting Possible Software Intrusion in FortiGate: Understanding Digital Signature Failures
Detecting Possible Software Intrusion in FortiGate: Understanding Digital Signature Failures In the cybersecurity landscape,...

Pablosec: Leading Cybersecurity in Ireland with Fortinet FCX Expertise
At Pablosec, we’re proud to set the benchmark for cybersecurity excellence in Ireland. As the only Fortinet partner in the...

Pablosec Partners with Proofpoint to Elevate Email Security and Threat Protection
Pablosec Partners with Proofpoint to Elevate Email Security and Threat Protection Pablosec is excited to announce its latest...
Pablosec Partners with Trellix to Boost Threat Detection and Response Capabilities
Pablosec Partners with Trellix to Elevate Threat Detection and Response Pablosec is proud to announce a new partnership with...

Pablosec Partners with Netskope to Secure Cloud Access and Data Protection
Pablosec Partners with Netskope to Enhance Secure Access to Cloud Services Pablosec is excited to announce a strategic...

Pablosec Partners with Zscaler to Boost Cloud Security
Pablosec Teams Up with Zscaler to Enhance Cloud Security Pablosec is proud to announce its new partnership with Zscaler, a...

Pablosec and Check Point Join Forces for Better Network Security
Pablosec Teams Up with Check Point to Enhance Network Security Pablosec, a leading cybersecurity consulting firm, is excited to...
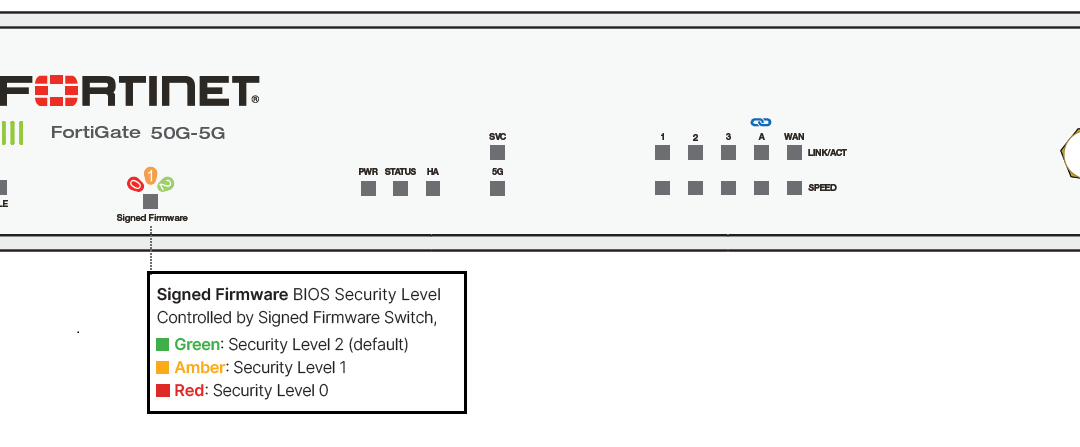
FortiGate 50G: New BIOS-Level Security LED and Physical Switch
Fortinet's latest release, the FortiGate 50G, introduces groundbreaking features that enhance network security and ease of...

Consulting 2.0: Pablosec Leading the Way in Cybersecurity Innovation
In today’s rapidly evolving digital landscape, traditional consulting models are no longer sufficient to address the complex...
