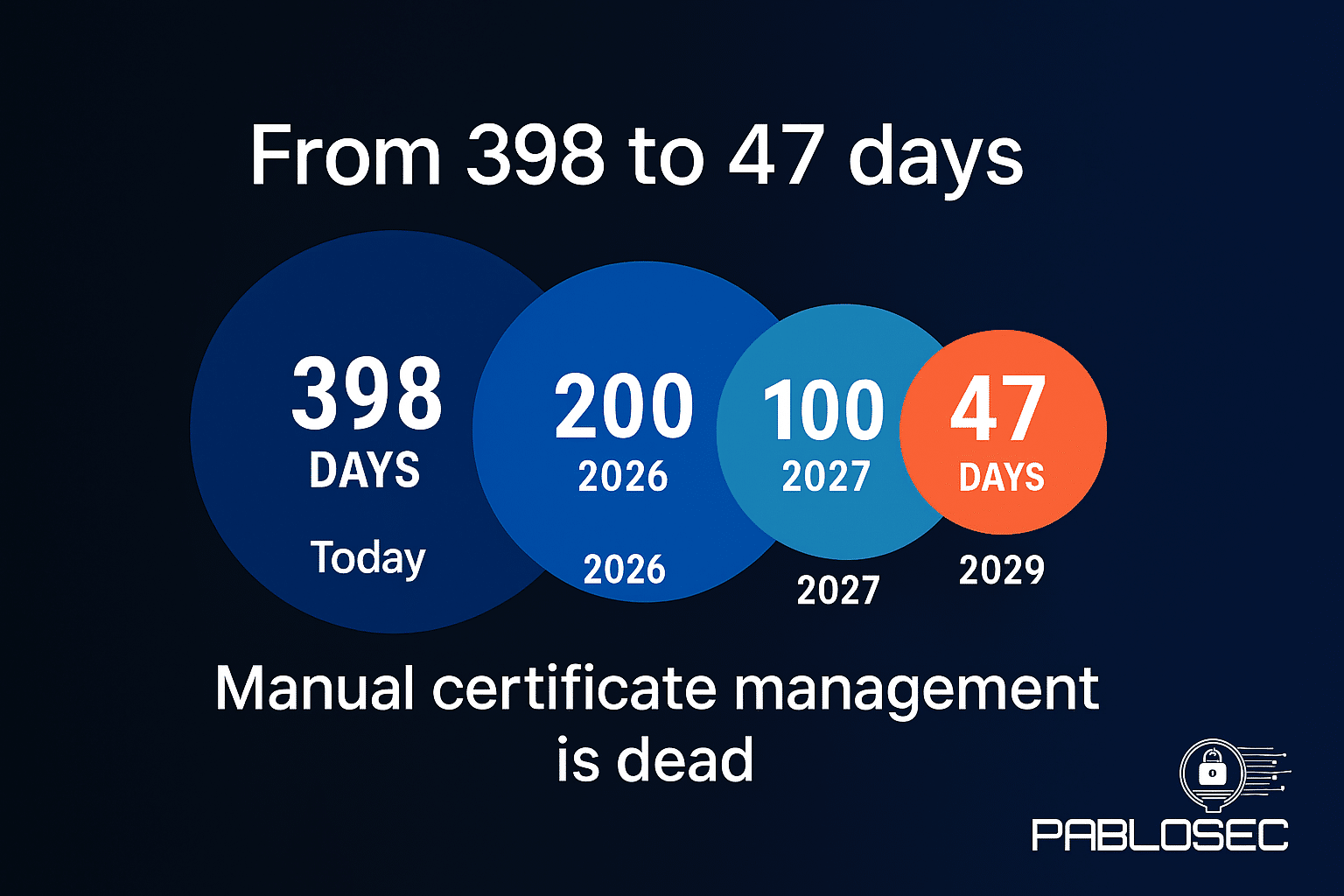
Digital certificates are the backbone of online trust. They secure websites, encrypt communications, and verify identities. For years, organizations have managed certificates with validity periods of one year or more.
But this is changing.
The global certificate ecosystem driven by the CA/Browser Forum and major browsers like Chrome, Safari, and Firefox has set a roadmap to shorten certificate lifetimes to just 47 days by 2029.
This isn’t just a technical update. It’s a transformation in how organizations must approach automation and security operations.
Why Move to 47-Day Certificates?
1. Reduce the risk window
Shorter lifetimes mean shorter exposure if a private key is compromised or misissued. The faster a certificate expires, the less time attackers have to exploit it.
2. Force automation and agility
At 47-day cycles, manual certificate management is impossible. Renewals, deployment, and monitoring must be automated. Spreadsheets and calendar reminders won’t cut it anymore.
3. Align with global trust policies
This change is not a DigiCert-only decision — it’s a global industry mandate. The CA/Browser Forum and browser vendors are pushing for shorter lifetimes to improve transparency, revocation speed, and overall trust. Every Certificate Authority (DigiCert, Sectigo, GlobalSign, etc.) must comply.
4. Prevent outages and trust failures
Expired certificates can cause outages, break critical services, and damage customer trust instantly. With shorter lifetimes, organizations that rely on manual processes will struggle to keep up.
What This Means for Organizations
- Comprehensive discovery: visibility into all certificates (internal, external, cloud, APIs).
-
Automated renewal & deployment: certificates must renew and deploy without human intervention.
-
Centralized monitoring: dashboards and alerts to prevent surprises.
-
Integrated response: SOAR (Security Orchestration, Automation, and Response) platforms will be key to orchestrate renewals and handle incidents.
-
Private PKI considerations: for internal services, some companies may shift to private PKI with different policies.
Final Thoughts
The move to 47-day certificate lifetimes is not a vendor choice — it’s a global standard in progress.
Organizations that prepare early by embracing automation and SOAR will navigate this transition smoothly. Those that remain dependent on manual processes risk outages, lost revenue, and reputational damage.
📌 The era of “install once, forget forever” is over. The future is fast, automated, and resilient certificate management.